Defence
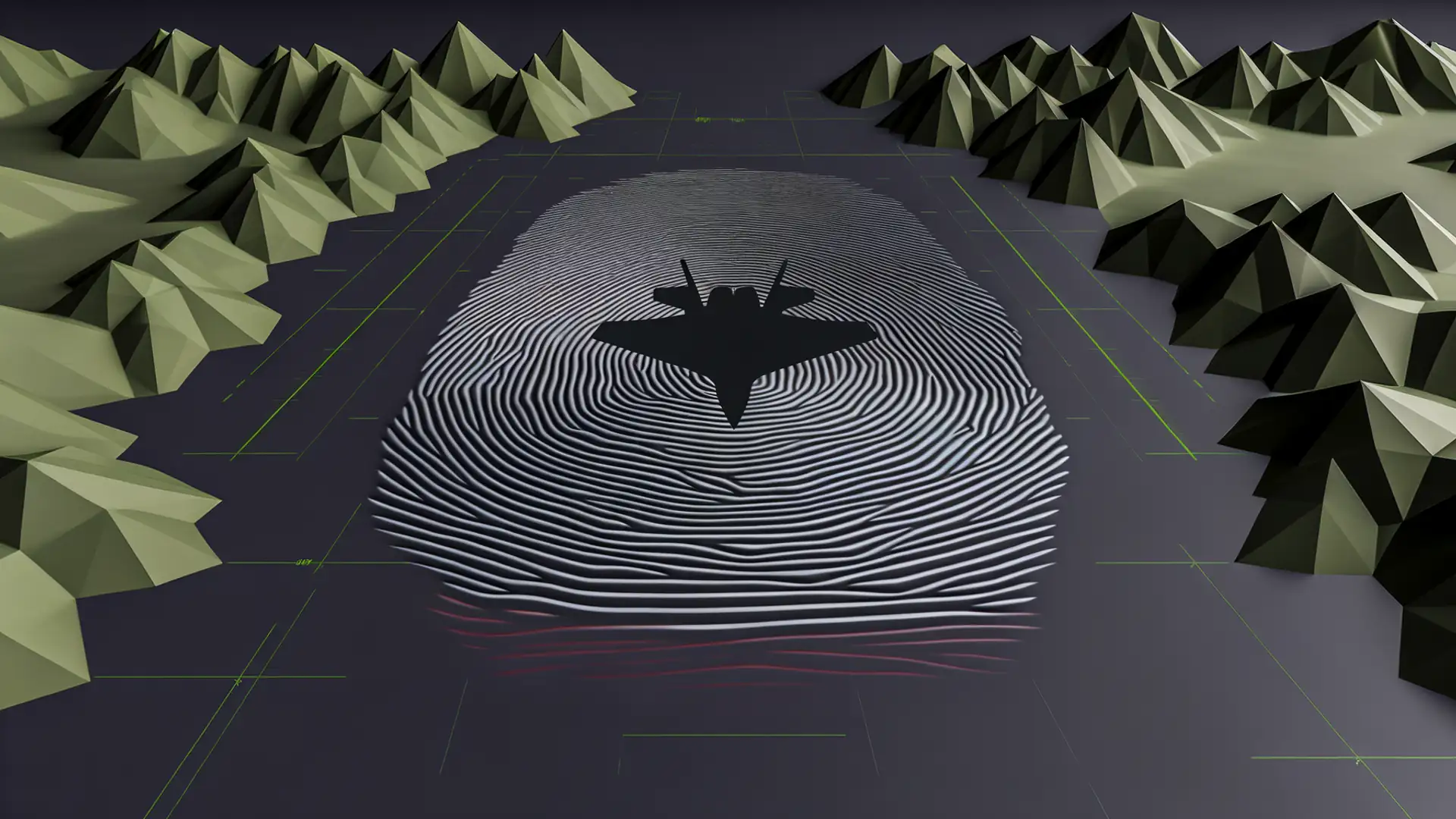
Verifiable trust infrastructure designed for defence environments
Defence and security organisations require trust infrastructure that operates without central authority dependency, preserves data sovereignty across national boundaries, and functions in classified-adjacent environments. This architectural approach is designed for those requirements.
Discuss defence trust infrastructureDefence organisations face three converging requirements: data sovereignty across multi-nation operations, secure communication in classified-adjacent environments, and interoperability between allied forces without creating centralised dependencies. Decentralised trust infrastructure -- where cryptographic verification operates at every organisational boundary -- is architecturally suited to these requirements. The same approach proven at scale in Swiss healthcare applies to defence communication, coalition data exchange, and sovereignty-preserving interoperability.
Regulatory drivers
NATO/EU Data Sovereignty
Multi-nation defence operations require trust infrastructure that preserves national data sovereignty while enabling verified communication between allied forces and institutions.
27 EU + 31 NATO member states with interoperability requirements
PESCO Cyber Capabilities
Permanent Structured Cooperation projects across EU defence focusing on cyber resilience, digital sovereignty, and the European Defence Technological and Industrial Base.
75 collaborative PESCO projects across EU defence
Cyber Resilience & Defence Supply Chains
Critical infrastructure protection extending to defence supply chains, requiring verifiable communication in classified-adjacent environments without centralised trust dependencies.
EUR 8 billion European Defence Fund 2021-2027
Solution overview
Verifiable trust infrastructure designed for defence environments means communication between organisations carries cryptographic proof of origin, integrity, and authorisation -- without depending on a central trust authority that could be compromised or operate outside national jurisdiction. This architectural capability preserves sovereignty by design: each participating organisation manages its own cryptographic identity while the infrastructure enables verified communication across boundaries.
See how it works →Proven at scale
Healthcare proved the architecture at scale. HIN -- operator of Switzerland's health information network -- processes over 800,000 verified messages per month through 850+ gateways serving 30,000+ healthcare institutions. The architectural properties that make this work -- decentralised key management, no single point of failure, sovereignty-preserving trust -- are the same properties that defence environments require for multi-nation interoperability.
800,000+
verified messages per month
850+
gateways across Swiss healthcare
30,000+
GP offices and healthcare institutions
Healthcare and defence share a fundamental architectural requirement: trust must operate across organisational boundaries without creating centralised dependencies. The infrastructure does not change -- the security context does.
Reference architecture
Click to expand diagram
How to engage
Work with Vereign directly
For organisations that want to scope and deploy trust infrastructure with Vereign's engineering and advisory team. Ideal for first movers and organisations with in-house technical capacity.
Explore services →Work through a partner
For organisations that prefer to work with a consultancy already trained on Vereign's trust infrastructure. Partners provide sector expertise alongside deployment capability.
See the partner programme →Team voices
We designed this architecture for environments where trust cannot depend on a single authority and data sovereignty is non-negotiable. Defence is the ultimate test of that principle -- every participating nation must retain control of its own cryptographic identity.
Explore trust infrastructure for defence environments
We can help you evaluate how decentralised trust infrastructure applies to your defence communication and interoperability requirements.