The Trust Infrastructure Landscape
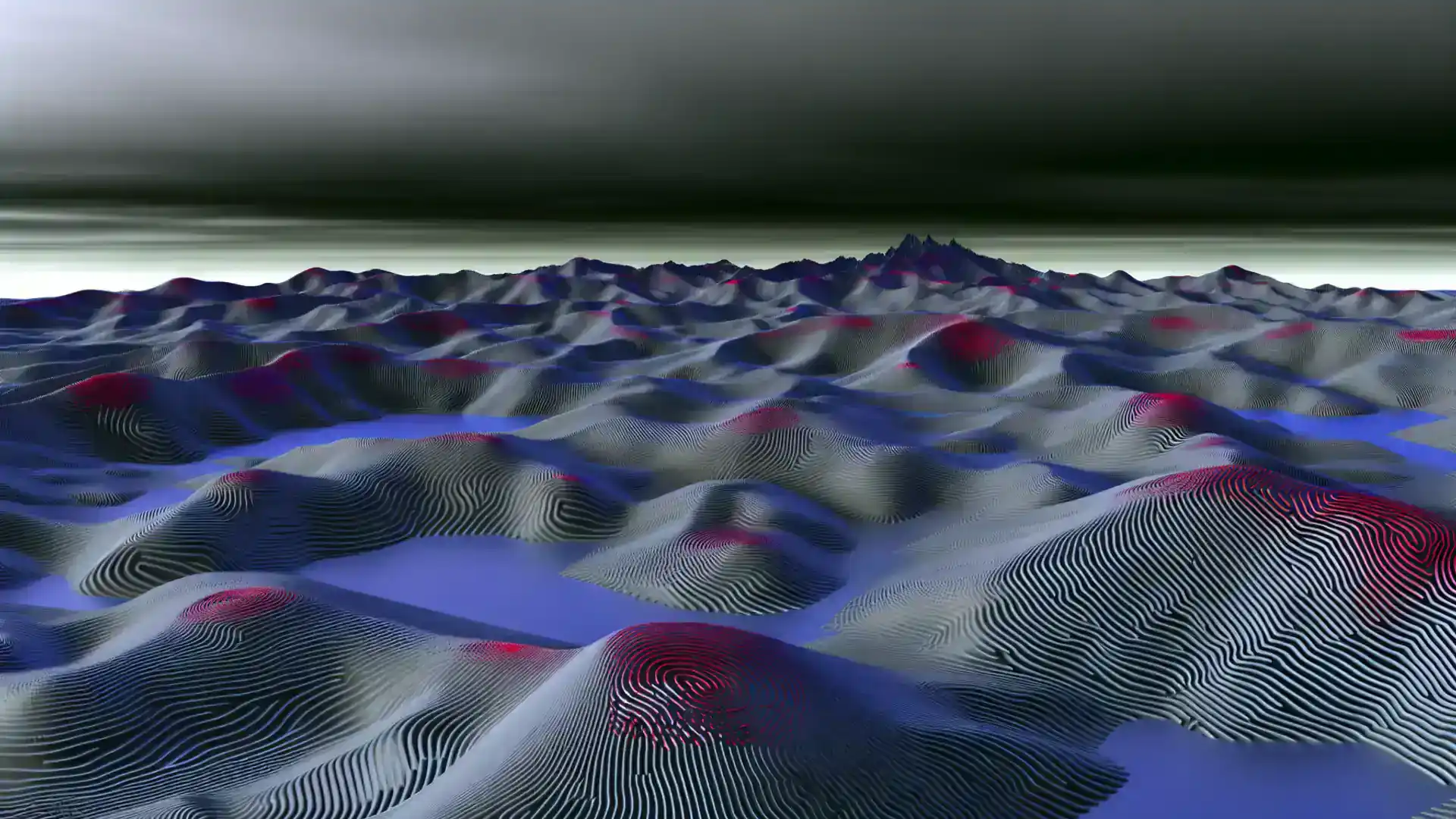
The trust infrastructure market has four distinct quadrants. Understanding where different approaches sit -- and what each means for your organisation -- is the first step in evaluating your options.
Assess your maturity levelMost organisations use identity management (who can access what) but few have invested in communication trust (verifying that every message is authentic, unaltered, and attributable). As regulatory requirements tighten across Europe, the gap between identity-only solutions and full communication trust becomes a strategic risk. This map shows where the major approaches sit.
The Four Quadrants of Trust Infrastructure
This framework maps the trust infrastructure landscape along two axes: the degree of centralisation (whether trust depends on a single authority) and the scope of trust (whether a solution covers identity only, or extends to full communication verification).
Click to expand diagram
Quadrant descriptions
Centralised Identity
Cloud-based identity and access management platforms excel at authenticating users and managing permissions across enterprise applications. They answer the question "who can access what?" with high reliability and scale.
Okta excels at workforce identity. CyberArk leads in privileged access management.
Distributed Identity
Emerging decentralised identity frameworks distribute credential verification across multiple parties, removing single points of failure from the identity layer. These approaches are gaining traction with eIDAS 2.0 and verifiable credentials.
Self-sovereign identity initiatives, EU Digital Identity Wallets.
Centralised Full Trust
Traditional PKI and HSM providers offer encryption, key management, and certificate-based trust through centralised infrastructure. They protect data in transit and at rest, but depend on central certificate authorities.
Thales provides PKI/HSM infrastructure with deep encryption heritage.
Distributed Full Communication Trust
Distributed trust infrastructure extends beyond identity to verify every message, track provenance, and provide compliance attestation -- without depending on a central authority. This is the emerging quadrant for organisations that need verifiable communication across organisational and national boundaries.
Vereign operates in this quadrant with decentralised key management (DKMS), message-level verification, and cross-border compliance attestation.
Distributed full communication trust is the only quadrant that can honor EHDS Article 71 opt-out end-to-end: consent withdrawal must propagate across every institution that holds derived data, which no central authority can cascade.
Read the consent architecture thesis$33B
IAM market size (2025)
Market Context
The identity and access management market alone is valued at $33 billion in 2025, growing at 10.4% annually. But identity is only one dimension of trust. As European regulations -- DORA, NIS2, EHDS, eIDAS 2.0 -- require verifiable communication integrity, organisations need solutions that go beyond "who logged in" to "is this message authentic and provably unaltered?" This gap becomes even more critical as AI systems reshape how decisions are made. Without verifiable data provenance, organisations cannot trust the inputs their AI systems consume -- or the outputs they produce. Authentic data is the prerequisite for trustworthy AI.
Where does your organisation sit?
Most organisations operate in the bottom-left quadrant -- strong identity, but no message-level trust. The Trust Infrastructure Maturity Model helps you understand your current position and what the next level looks like.
Take the self-assessmentExplore the trust infrastructure landscape
Whether you are evaluating trust infrastructure for a specific sector or exploring partnership opportunities, we can help you navigate the landscape.